Top
Secure, compliant and efficient access to criminal history record databases and critical workflows for police departments, sheriffs’ offices and other law enforcement agencies.
Drivers in Law Enforcement IT Security
As police and law enforcement agencies adopt new mobile technologies, the risk of unauthorized access to record databases that store sensitive citizen data, criminal history, fingerprint records and motor vehicle information grows. With officers on patrol and at desks, efficient and easy access to these records is critical. Tight budgets and IT resources need scalable solutions to support growing needs. In addition, mandates and standards require the use of multi-factor and risk-based authentication methods.
HID® DigitalPersona® helps federal, state and local law enforcement agencies to:
- Establish secure user identities in alignment with a Zero Trust security approach
- Comply with CJIS Security Policy for two-factor (2FA) or advanced multi-factor authentication (MFA) from remote or unsecured locations
- Deploy the right authentication factor that meets the needs of your individual user—whether it’s a biometric, mobile access, tokens, smart cards, or One-Time Passwords, we have you covered
- Defend against data breach with granular policy control that is consistently enforced whether officers are at a desk or out on patrol
- Easily scale mobile security with an adaptable and scalable authentication solution that covers any device, anytime and anywhere with limited burden to IT infrastructure and support teams
- Balance security and convenience with a broad selection of authentication methods that allows for both strong data security and frictionless access
- Deploy rapidly in days, not months, and with minimal disruption to both IT and end users
- Implement customized solutions for the unique needs of your law enforcement agency using HID Professional Services

Secure Access for All Apps and Devices
Databases storing criminal history, fingerprint records and motor vehicle information can be securely accessed from all endpoints including mobile, squad car laptop or precinct desktop. Authentication policies are consistent across devices and locations, whether officers are at a desk or on patrol.
Balance Security and Convenience
Law enforcement agencies have the flexibility to deploy contextually appropriate authentication methods whenever and wherever needed. System administrators can manage customizable authentication schemes on the fly with an array of traditional and risk-based factors.
Rapid Adaptability With Full Compliance
Deploy in days with little to no disruption to agency operations. Compliant data and network security with the CJIS standard for advanced multi-factor authentication and alignment to NIST 800-63 digital identity guidelines is made simple.



Security and Mobility With Panasonic Toughbook®
The inclusion of HID DigitalPersona with the Toughbook delivery is an extremely powerful and secure mobile computing solution. DigitalPersona seamlessly provides a flexible range of authentication methods for granting secure access to the laptop, applications and workflows, whether local or in the cloud.
Industry Leading Experience
HID has decades of experience in delivering advanced identity solutions in the government space for employees, citizens and contractors. We've implemented advanced multi-factor authentication solutions in some of the most complex IT environments and trusted by:




Read HID DigitalPersona User Reviews
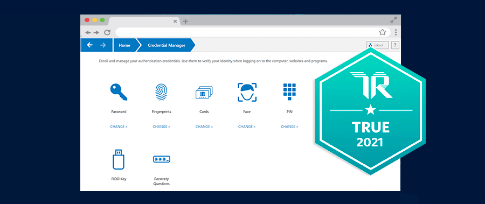 HID DigitalPersona® is Now TRUE Certified
HID DigitalPersona® is Now TRUE Certified
See why we were awarded the TrustRadius TRUE certification for authentic feedback >>
 BLOG: Approaches to Identity and Access Management for Local Governments, Employees and Citizens
BLOG: Approaches to Identity and Access Management for Local Governments, Employees and Citizens
Discover the best methods for approaching IAM supported by relevant policies, training, and compliance >>